access control card administration A badge access control system is a security solution that manages who can enter your building or specific areas within it. It uses electronic badges or keycards to ensure that only authorized individuals—like employees or . To enable NFC Tag Reader functionality on these models, you need to access the Control Center and activate the NFC Tag Reader manually. To add the NFC Tag Reader option in the Control Center, use these steps: 1. .
0 · wireless access control card readers
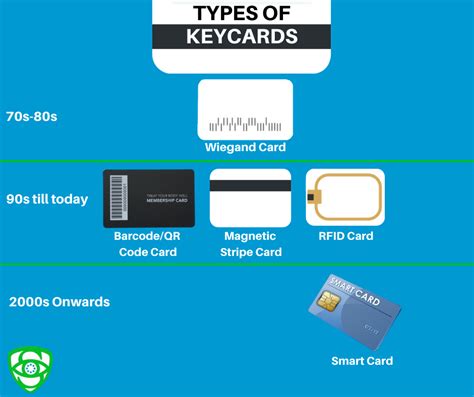
1 · types of access control cards
2 · card access control systems companies
3 · best key card access systems
4 · access control proximity cards
5 · access control card printers
6 · access control card calculator
7 · access card issuance daily monitoring
FeliCa RC-S380 desktop USB reader The FeliCa RC-S380 from Sony is the world's first NFC .
Access control management is implementing tools, processes, and policies to ensure that each entity can and does access only the appropriate data and systems. What are the three types of access control? Three of the most common types of access control are: Rule-based .

machine to insert rfid to woven label
A badge access control system is a security solution that manages who can enter your building or specific areas within it. It uses electronic badges or keycards to ensure that only authorized individuals—like employees or .How can you use proximity reader access control technology to safeguard your facility? In this . Everything you need to know about RBAC in one place. This article provides a .
wireless access control card readers
Card access control systems have transformed security management across various sectors, . Access control management is implementing tools, processes, and policies to ensure that each entity can and does access only the appropriate data and systems. What are the three types of access control? Three of the most common types of access control are: Rule-based access control (RuBAC) Role-based access control (RBAC)
A badge access control system is a security solution that manages who can enter your building or specific areas within it. It uses electronic badges or keycards to ensure that only authorized individuals—like employees or approved visitors—can enter secure spaces. When someone scans their badge at a reader, the system verifies their access. The EPS Managed Access administrators are able to manage cards, records, and many other programming needs. They can add new employees, and remove former ones, set specific activation dates or deactivate access cards, and even limit access to .How can you use proximity reader access control technology to safeguard your facility? In this article, we will discuss what proximity readers are, how an proximity access control system works, different types of door key card reader configurations and other considerations you must know before you install these devices in your facility. Everything you need to know about RBAC in one place. This article provides a comprehensive overview of role-based access control (RBAC) along with a guided approach to implementing, maintaining, and extending RBAC to suit the needs of your organization.
types of access control cards
card access control systems companies
Card access control systems have transformed security management across various sectors, offering unparalleled control and protection. These systems utilize advanced technology to regulate access based on the credentials embedded within access cards.

Cybercriminals are becoming more sophisticated, utilizing advanced techniques to breach security systems and gain unauthorized access to resources. Access control is a proactive security measure that helps deter, detect, and prevent unauthorized access.
Access cards are the backbone of most card access control systems, providing a secure and convenient way to manage entry into buildings and secure areas. These cards, often the size of a credit card, hold essential data to grant or deny access.
Access control is an essential element of security that determines who is allowed to access certain data, apps, and resources—and in what circumstances. In the same way that keys and preapproved guest lists protect physical spaces, access control policies protect digital spaces. Badge and ID card access control systems ensure that only authorized individuals can enter secured facilities, provide audit trails for regulatory compliance and incident investigations, and support administrators by allowing them to easily add, modify, or remove privileges associated with users. Access control management is implementing tools, processes, and policies to ensure that each entity can and does access only the appropriate data and systems. What are the three types of access control? Three of the most common types of access control are: Rule-based access control (RuBAC) Role-based access control (RBAC) A badge access control system is a security solution that manages who can enter your building or specific areas within it. It uses electronic badges or keycards to ensure that only authorized individuals—like employees or approved visitors—can enter secure spaces. When someone scans their badge at a reader, the system verifies their access.
The EPS Managed Access administrators are able to manage cards, records, and many other programming needs. They can add new employees, and remove former ones, set specific activation dates or deactivate access cards, and even limit access to .How can you use proximity reader access control technology to safeguard your facility? In this article, we will discuss what proximity readers are, how an proximity access control system works, different types of door key card reader configurations and other considerations you must know before you install these devices in your facility.
Everything you need to know about RBAC in one place. This article provides a comprehensive overview of role-based access control (RBAC) along with a guided approach to implementing, maintaining, and extending RBAC to suit the needs of your organization.Card access control systems have transformed security management across various sectors, offering unparalleled control and protection. These systems utilize advanced technology to regulate access based on the credentials embedded within access cards.
Cybercriminals are becoming more sophisticated, utilizing advanced techniques to breach security systems and gain unauthorized access to resources. Access control is a proactive security measure that helps deter, detect, and prevent unauthorized access. Access cards are the backbone of most card access control systems, providing a secure and convenient way to manage entry into buildings and secure areas. These cards, often the size of a credit card, hold essential data to grant or deny access.Access control is an essential element of security that determines who is allowed to access certain data, apps, and resources—and in what circumstances. In the same way that keys and preapproved guest lists protect physical spaces, access control policies protect digital spaces.
best key card access systems
access control proximity cards
NFC, as the name implies, is near-field. These tags require the phone’s magnetic field to power .
access control card administration|best key card access systems