what security issues are associated with rfid tags This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily. Tapping to pay with your Visa contactless card or payment-enabled mobile/wearable device is .A contactless smart card is a contactless credential whose dimensions are credit card size. Its embedded integrated circuits can store (and sometimes process) data and communicate with a terminal via NFC. Commonplace uses include transit tickets, bank cards and passports. There are two broad categories of . See more
0 · rfid security problems
1 · rfid privacy and security issues
2 · rfid is vulnerable to
3 · rfid disadvantages
4 · problems with rfid technology
5 · problems with rfid
6 · is rfid dangerous
7 · compliance issues with rfid bands
NFC stands for Near Field Communication and has three operating modes: card emulation, .
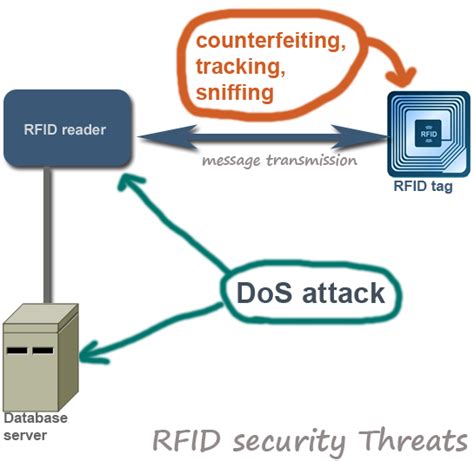
This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; . The use of RFID tags to track humans has been met with resistance due to privacy concerns. Poor physical security can result in tags being destroyed even if there is no specific gain for the attacker, leading to further risks associated with RFID technology.This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily. The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in knowing that attacks on RFID systems aren’t easy to penetrate.
Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of .

RFID tags can be read if the reader is nearby, even if a bar code would be obscured. RFID tags can be used for tracking packages in the mail or goods in a warehouse. The RFID tag can contain tracking information or just a unique identification code.Rather than retrofitting RFID systems to respond to privacy and security issues, it is much preferable that privacy and security should be designed in from the beginning. Consumer Transparency : There should be no secret RFID tags or readers.
The results are discussed in the following sections: the first is the Applications Section, whose subsections are the Internet of Things (IoT), Supply Chain Management, Localization, Traceability, Logistics, Ubiquitous Computing, Healthcare, and Access Control; the second is the Security and Privacy section, whose subsections are Authentication,. Personnel identification: In many business applications, humans (employees, clients, patients, visitors, etc) are identified through information generated from associated barcode or RFID tag. The security issues are more focused on the privacy issues related to the tagged personnel. The list includes an assortment of common security problems such as spoofing, skimming, eavesdropping, sniffing, denial-of-service, physical attacks, traffic analysis, and. Part 2 examines some of the more common security and privacy concerns associated with RFID, primarily related to retail and consumer applications. What is RFID?
rfid security problems
The use of RFID tags to track humans has been met with resistance due to privacy concerns. Poor physical security can result in tags being destroyed even if there is no specific gain for the attacker, leading to further risks associated with RFID technology.This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily. The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in knowing that attacks on RFID systems aren’t easy to penetrate.
Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of . RFID tags can be read if the reader is nearby, even if a bar code would be obscured. RFID tags can be used for tracking packages in the mail or goods in a warehouse. The RFID tag can contain tracking information or just a unique identification code.Rather than retrofitting RFID systems to respond to privacy and security issues, it is much preferable that privacy and security should be designed in from the beginning. Consumer Transparency : There should be no secret RFID tags or readers. The results are discussed in the following sections: the first is the Applications Section, whose subsections are the Internet of Things (IoT), Supply Chain Management, Localization, Traceability, Logistics, Ubiquitous Computing, Healthcare, and Access Control; the second is the Security and Privacy section, whose subsections are Authentication,.
Personnel identification: In many business applications, humans (employees, clients, patients, visitors, etc) are identified through information generated from associated barcode or RFID tag. The security issues are more focused on the privacy issues related to the tagged personnel.
The list includes an assortment of common security problems such as spoofing, skimming, eavesdropping, sniffing, denial-of-service, physical attacks, traffic analysis, and.
dstv smart card number example
cable one smart card mute
rfid privacy and security issues
rfid is vulnerable to
It has never been easier to read and write NFC cards on your computer ;)-----• .
what security issues are associated with rfid tags|rfid privacy and security issues