rfid attack methods tracking By reading information received from RFID tag an attacker can track the location and movement of an object or a person. When a tag is attached to an object and the object enter the RFID reader’s field, the RFID read can identify the object and locate its position. USB NFC reader that follows ISO 14443 and ISO 18092. USB NFC reader that .
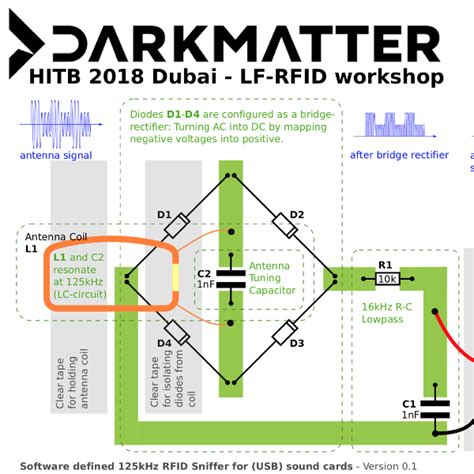
0 · sniffing rfid
1 · rfid tracking
2 · rfid systems
3 · rfid security threats
4 · rfid security problems
5 · rfid hacking protection
6 · rfid hacking examples
7 · rfid hacking definition
Relay: Relays NFC traffic between two devices using a server. One device operates as a .Google Pay / Google Wallet (one or both, depending on where you are) do NOT allow cloning cards. They let you register a legitimate bank card or credit card with Google, which your phone uses for tap-to-pay. It doesn't pretend to be your card, it sends a secure token which is later .
The most common techniques include: Active Jamming. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. .
There are several ways in which RFID hacking can occur: Eavesdropping: Attackers intercept . The most common techniques include: Active Jamming. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos .There are several ways in which RFID hacking can occur: Eavesdropping: Attackers intercept and decode the radio signals exchanged between the tags and readers, gaining unauthorized access to sensitive information. RFID Cloning: Hackers clone legitimate RFID tags and use them to gain unauthorized access to restricted areas or valuable assets.By reading information received from RFID tag an attacker can track the location and movement of an object or a person. When a tag is attached to an object and the object enter the RFID reader’s field, the RFID read can identify the object and locate its position.
A common way to defeat a spoofing attack is to implement an RFID authentication protocol and data encryption, which increases the cost and technology complexity needed for a successful attack.
sniffing rfid
rfid tracking
While RFID technology has many benefits, such as asset tracking and supply chain management, it also presents vulnerabilities that malicious actors can exploit. This article will explore the basics of RFID technology, the potential threats posed by RFID attacks, and the best practices for protecting against them. Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful. RFID technology is the core technology of the perception layer of the Internet of Things, which can realize the real-time transmission of information between ob.In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security.
This study provides an overview of RFID technology. This study aims to identify potential vulnerabilities in RFID-related physical controls in an infrastructure. This includes evaluating the effectiveness of encryption algorithms, frequency range and band, and RFID type. 1 Introduction. RFID is expected to be the basic technology for ubiquitous network or computing, and to be associated with other technology such as telemetric, and wireless sensors. Recently, the wide deployment of RFID systems in a variety of applications has raised many concerns about the privacy and the security issues. The most common techniques include: Active Jamming. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos .
There are several ways in which RFID hacking can occur: Eavesdropping: Attackers intercept and decode the radio signals exchanged between the tags and readers, gaining unauthorized access to sensitive information. RFID Cloning: Hackers clone legitimate RFID tags and use them to gain unauthorized access to restricted areas or valuable assets.By reading information received from RFID tag an attacker can track the location and movement of an object or a person. When a tag is attached to an object and the object enter the RFID reader’s field, the RFID read can identify the object and locate its position.
rfid systems
A common way to defeat a spoofing attack is to implement an RFID authentication protocol and data encryption, which increases the cost and technology complexity needed for a successful attack.While RFID technology has many benefits, such as asset tracking and supply chain management, it also presents vulnerabilities that malicious actors can exploit. This article will explore the basics of RFID technology, the potential threats posed by RFID attacks, and the best practices for protecting against them.
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful. RFID technology is the core technology of the perception layer of the Internet of Things, which can realize the real-time transmission of information between ob.In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security. This study provides an overview of RFID technology. This study aims to identify potential vulnerabilities in RFID-related physical controls in an infrastructure. This includes evaluating the effectiveness of encryption algorithms, frequency range and band, and RFID type.
barcode reader nfc

rfid security threats
NFL playoff predictions: Picking 8 division winners, 6 wild-card teams at midpoint of 2024 season. Published: Nov 06, 2024 at 02:52 PM. Playoff picks. Super Bowl predictions. .
rfid attack methods tracking|rfid hacking protection