rfid reader tries Once the reader has received the tag’s data, it must be interpreted correctly. The reader interprets the data by combining the object identifier obtained from the tag with context provided by other tag readings, sensor information, business rules, and other . See more AUBURN, Ala.— The 2023 Auburn football season will introduce several new .
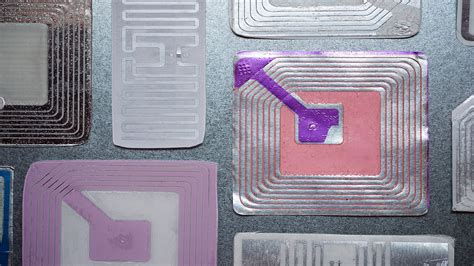
0 · what does rfid look like
1 · rfid is involved when using
2 · radio frequency identification rfid technology
3 · radio frequency identification reader
4 · how to use rfid tags
5 · how to use rfid scanner
6 · how does rfid scanning work
7 · how do rfid tags work
Listen to Stream Auburn Tigers here on TuneIn! Listen anytime, anywhere! Home. Search. Local Radio. Recents. Trending. Music. Sports. News & Talk. Podcasts. By Location. By Language. . ESPN Sports Radio for Birmingham. .
RFID tags and readers communicate through the modulation of radio waves. This communication occurs by changing the amplitude of radio waves through Amplitude Shift Keying (ASK). See more
Through coding, The 1’s and 0’s (bits) of binary code translate into radio transmissions through Amplitude Shift Keying. In the case . See more
Medium Access Control is how RFID systems ensure that signal only comes from one tag at a time. Although many RFID interactions . See more
A command indicates the kind of data the reader requests from the tag. Command sets communicate between reader and tag through a standard format called a packet. A packet can be 1-150 bits of data separated into a preamble, a command, a parameter, and an . See more
Once the reader has received the tag’s data, it must be interpreted correctly. The reader interprets the data by combining the object identifier obtained from the tag with context provided by other tag readings, sensor information, business rules, and other . See more
2023 Product Catalog. Transponder & Reader Engineered Systems, Inc. is an RFID development group. With our TRES433 Active and TRES900 Passive UHF products, it is our mission to . RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is . If a reader tries to communicate with multiple tags at once, it will indicate the timing at which a tag should transmit its data through the MAC. The two types of MACs commonly .2023 Product Catalog. Transponder & Reader Engineered Systems, Inc. is an RFID development group. With our TRES433 Active and TRES900 Passive UHF products, it is our mission to .
RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is . Learn how to effectively use an RFID reader to improve security and streamline operations in your business. Discover tips and best practices for successful implementation. Here are the 6 factors that most commonly affect RFID read range. Contents. RFID Antenna Selection – Gain, Beamwidth. RFID Tag Selection and Positioning – Size, .
An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your .An RFID card reader is a device that can read information stored on an RFID tag or card. It mainly consists of antennas, radio frequency modules, control units, and interface circuits. How-To & Best Practices. How to Test an RFID System. Here are eight steps to ensure a successful pilot of radio frequency identification technologies. Published: March 8, . By implementing RFID readers, businesses can benefit from improved inventory control, enhanced supply chain visibility, reduced errors, and enhanced customer experiences. .
Make a remote work logger using an RFID reader and a GPS module. Scan a card and get ID, location, and time. All the perfect data to punch in and punch out from the middle of Nowhere!
smart card manufacturing company
If a reader tries to communicate with multiple tags at once, it will indicate the timing at which a tag should transmit its data through the MAC. The two types of MACs commonly .
2023 Product Catalog. Transponder & Reader Engineered Systems, Inc. is an RFID development group. With our TRES433 Active and TRES900 Passive UHF products, it is our mission to . RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is .
what does rfid look like
Learn how to effectively use an RFID reader to improve security and streamline operations in your business. Discover tips and best practices for successful implementation. Here are the 6 factors that most commonly affect RFID read range. Contents. RFID Antenna Selection – Gain, Beamwidth. RFID Tag Selection and Positioning – Size, .An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your .
An RFID card reader is a device that can read information stored on an RFID tag or card. It mainly consists of antennas, radio frequency modules, control units, and interface circuits. How-To & Best Practices. How to Test an RFID System. Here are eight steps to ensure a successful pilot of radio frequency identification technologies. Published: March 8, . By implementing RFID readers, businesses can benefit from improved inventory control, enhanced supply chain visibility, reduced errors, and enhanced customer experiences. .
rfid is involved when using
radio frequency identification rfid technology
TIGER TALK. Thursdays at 6 p.m. CT. Hosted by Brad Law and the Voice of the Tigers, Andy Burcham, weekly guests will include head football coach Hugh Freeze in the fall .
rfid reader tries|how do rfid tags work