attacks cannot be carried out against smart cards We propose a novel attack that bypasses the jamming signal emitted by a blocking card and reads the content of the smart card. We evaluate the effectiveness of 11 blocking cards when . $23.00
0 · Smart Card Security
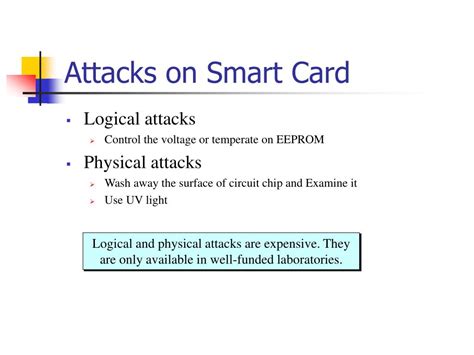
1 · Section 5
2 · Overview about attacks on smart cards
3 · Invasive Attacks
4 · Hardware
5 · Beware of Pickpockets: A Practical Attack against Blocking Cards
6 · Attacking smart card systems: Theory and practice
7 · Application of Attack Potential to Smartcards and Similar
Visit ESPN for the complete 2024 NFL season standings. Includes league, conference and division standings for regular season and playoffs.
We propose a novel attack that bypasses the jamming signal emitted by a blocking card and reads the content of the smart card. We evaluate the effectiveness of 11 blocking cards when .It may not be necessary to carry out all of the experiments to identify the full attack, provided it is clear that the attack actually proves that access has been gained to a TOE asset, and that the .
This article provides a brief overview of selected attacks on smart cards, and also examines cases where real world systems using smart cards were attacked because of factors .
setool smart card driver windows 7 64-bit
This article examines the range of possible attacks against smart cards, and the measures that can be used to protect against these attacks. It then investigates the security attacks on confidentiality, integrity, and availability of data in smart card–based systems and applications, including unauthorized remote .There is a wide range of software attacks, some of which are not specific to the smart card. Incorrect file access conditions, malicious code, flaws in cryptographic protocols, design and .However, increasing use of smart cards has made them vulnerable to a large number of security attacks that are of specialized or general nature. In this chapter, we discuss various security .
DPA can be carried out successfully against most smart cards currently in production. DPA is a complicated attack that relies on statistical inferences drawn on power consumption data .
Smart Card Security
. In this work, we analyse two well-known classes of physical attacks-fault injections and side-channel attacks-and their application to mobile devices. Such attacks are . The essential property of a smart card is its ability to offer a secure environment for data and programs. This article examines the range of possible attacks against smart cards, and the measures that can be used to protect against these attacks.

We propose a novel attack that bypasses the jamming signal emitted by a blocking card and reads the content of the smart card. We evaluate the effectiveness of 11 blocking cards when protecting a MIFARE Ultralight smart card and a MIFARE Classic card.It may not be necessary to carry out all of the experiments to identify the full attack, provided it is clear that the attack actually proves that access has been gained to a TOE asset, and that the complete attack could
This article provides a brief overview of selected attacks on smart cards, and also examines cases where real world systems using smart cards were attacked because of factors not directly related to the security of the actual token.
This article examines the range of possible attacks against smart cards, and the measures that can be used to protect against these attacks. It then investigates the security attacks on confidentiality, integrity, and availability of data in smart card–based systems and applications, including unauthorized remote monitoring, communication protocol exploitation, denial of service (DoS) attacks, and so forth, and presents the possible countermeasures for these attacks.
There is a wide range of software attacks, some of which are not specific to the smart card. Incorrect file access conditions, malicious code, flaws in cryptographic protocols, design and implementation errors are common flaws in computing systems.
However, increasing use of smart cards has made them vulnerable to a large number of security attacks that are of specialized or general nature. In this chapter, we discuss various security attacks on hardware and software components of smart cards in detail and present appropriate countermeasures for these attacks.DPA can be carried out successfully against most smart cards currently in production. DPA is a complicated attack that relies on statistical inferences drawn on power consumption data measured during smart card computation. . In this work, we analyse two well-known classes of physical attacks-fault injections and side-channel attacks-and their application to mobile devices. Such attacks are well-understood.
The essential property of a smart card is its ability to offer a secure environment for data and programs. This article examines the range of possible attacks against smart cards, and the measures that can be used to protect against these attacks.We propose a novel attack that bypasses the jamming signal emitted by a blocking card and reads the content of the smart card. We evaluate the effectiveness of 11 blocking cards when protecting a MIFARE Ultralight smart card and a MIFARE Classic card.
set smart talk card readers reader plus 3 card boxes
It may not be necessary to carry out all of the experiments to identify the full attack, provided it is clear that the attack actually proves that access has been gained to a TOE asset, and that the complete attack could This article provides a brief overview of selected attacks on smart cards, and also examines cases where real world systems using smart cards were attacked because of factors not directly related to the security of the actual token. This article examines the range of possible attacks against smart cards, and the measures that can be used to protect against these attacks. It then investigates the security attacks on confidentiality, integrity, and availability of data in smart card–based systems and applications, including unauthorized remote monitoring, communication protocol exploitation, denial of service (DoS) attacks, and so forth, and presents the possible countermeasures for these attacks.

There is a wide range of software attacks, some of which are not specific to the smart card. Incorrect file access conditions, malicious code, flaws in cryptographic protocols, design and implementation errors are common flaws in computing systems.However, increasing use of smart cards has made them vulnerable to a large number of security attacks that are of specialized or general nature. In this chapter, we discuss various security attacks on hardware and software components of smart cards in detail and present appropriate countermeasures for these attacks.
Section 5
Overview about attacks on smart cards
DPA can be carried out successfully against most smart cards currently in production. DPA is a complicated attack that relies on statistical inferences drawn on power consumption data measured during smart card computation.
sd card for lg smart phone
Invasive Attacks
One of the following options, must be selected -. Debit Card, Credit Card, .
attacks cannot be carried out against smart cards|Attacking smart card systems: Theory and practice