authentication method for smart cards If you use a smart card, the operating system uses Kerberos v5 authentication . The "NFL 100 Greatest" ranks the top 100 games in NFL history, and the Green Bay Packers vs. San Francisco 49ers clash in the 1998 NFC Wild Card lands at No. 46. "NFL 100 Greatest" counts down the .
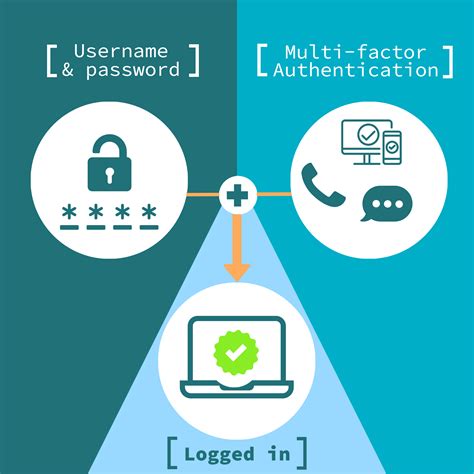
0 · smart card multi factor authentication
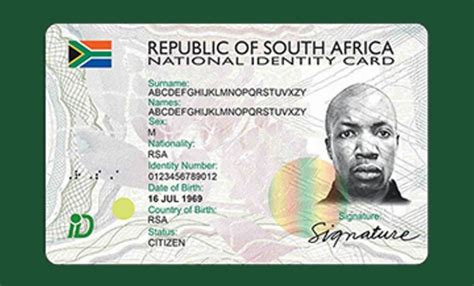
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
Buy NFC Card Reader Writer, Card Copier NFC Card Reader Kit 512kb Memory IC .
If you use a smart card, the operating system uses Kerberos v5 authentication .
rfid chip auslesen iphone
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
smart card multi factor authentication
Give smart cards to approved users and help them turn on the cards, choose a secret code, and use the cards properly. Provide classes and help for users to learn about smart card logins and get answers to questions or worries. Password-based authentication is the most common and simplest method of authentication for securing your network monitoring program. Here, the "password" might be a username-password combination, passcode, or PIN. It's intuitive, as many users are already familiar with such login methods.
This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears . Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the user's authentication credentials, such as a personal identification number (PIN), digital certificates, and biometric data.
smart card identity
smart card based identification system
Smartcard authentication is the first passwordless authentication method ever created, it is based on X509 certificates and has been used by governments around the world for over 2 decades. Smartcard authentication is the most secure authentication method available today; however, it is also the most complex to implement and manage.

How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.
Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications. Give smart cards to approved users and help them turn on the cards, choose a secret code, and use the cards properly. Provide classes and help for users to learn about smart card logins and get answers to questions or worries. Password-based authentication is the most common and simplest method of authentication for securing your network monitoring program. Here, the "password" might be a username-password combination, passcode, or PIN. It's intuitive, as many users are already familiar with such login methods.This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.
Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the user's authentication credentials, such as a personal identification number (PIN), digital certificates, and biometric data.
smart card authentication step by
smart card authentication protocol
RFID PVC ISO card IC: [HF] Broadcom Topaz 512 (BCM20203T512Topaz) Operating .
authentication method for smart cards|enable smart card log on