power analysis attacks on smart cards The basic power attack is presented: simple power analysis. It directly exploits the dependency . Locate the power button on the right side of the phone. 2. Press and hold the power button until the Motorola logo appears on the screen. 3. Release the power button once the logo appears. .
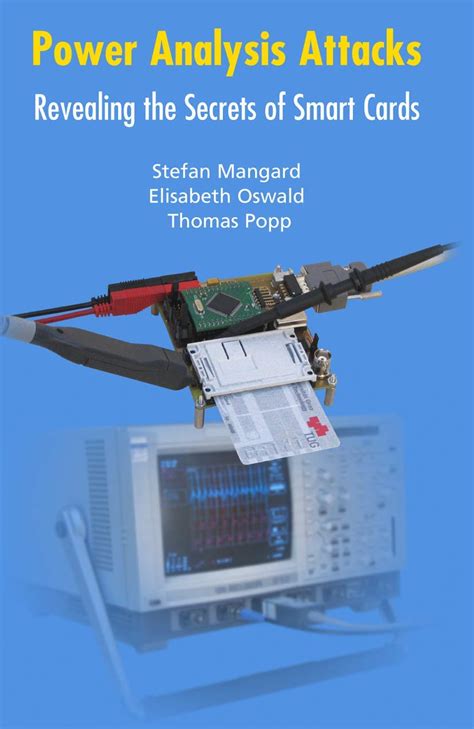
0 · \Power Analysis Attacks: Revealing the Secrets of Smart Cards"
1 · Power analysis attacks : revealing the secrets of smart cards
2 · Power Analysis Attacks: Revealing the Secrets of Smart Cards
3 · Power Analysis Attacks : Revealing the Secrets of Smart Cards
Step 1: Go to Settings on your phone. Step 2: Select Apps and then click on See all apps. Step 3: Next, choose NFC service from the list. Step 4: Click on Storage. Step 5: Now click on the Clear Cache button that appears. .
The basic power attack is presented: simple power analysis. It directly exploits the dependency .
Power analysis attacks : revealing the secrets of smart cards. 1. Introduction -- 2. .The first comprehensive discussion of power analysis attacks on smart cards. Examples and . Power Analysis Attacks: Revealing the Secrets of Smart Cards is the first .
The basic power attack is presented: simple power analysis. It directly exploits the dependency between the power consumption (i.e. patterns in the power trace) and secret information. Power analysis attacks : revealing the secrets of smart cards. 1. Introduction -- 2. Cryptographic devices -- 3. Power consumption -- 4. Statistical characteristics of power traces -- 5. Simple power analysis -- 6. Differential power analysis -- 7. Hiding -- 8.The first comprehensive discussion of power analysis attacks on smart cards. Examples and case studies illustrate the various attacks, from simple to differential power-analysis attacks. Detailed descriptions and comparisons of the effectiveness of different countermeasures. Power Analysis Attacks: Revealing the Secrets of Smart Cards is the first comprehensive treatment of power analysis attacks and countermeasures. Based on the principle that the.
Power Analysis Attacks: Revealing the Secrets of Smart Cards provides a unified overview and comparison of power analysis attacks. Illustrative examples and case studies are used throughout the monograph to explain the attacks and compare the effectiveness of the different countermeasures. This volume explains how power analysis attacks work and provides an extensive discussion of countermeasures like shuffling, masking, and DPA-resistant logic styles to decide how to protect smart cards. Power analysis attacks .Power analysis attacks allow the extraction of secret information from smart cards. Smart cards are used in many applications including banking, mobile communications, pay TV, and electronic signatures. In all these applications, the security of the smart cards is of crucial importance.
Power Analysis Attacks - Revealing the Secrets of Smart Cards — Graz University of Technology. Stefan Mangard, Maria Elisabeth Oswald, Thomas Popp. Institute of Applied Information Processing and Communications (7050) Research output: Book/Report › Book. Overview. Projects (6) Treatment code (Nähere Zuordnung) Application. Theoretical. Power Analysis Attacks: Revealing the Secrets of Smart Cards is the first comprehensive treatment of power analysis attacks and countermeasures. Based on the principle that the. This volume explains how power analysis attacks work and provides an extensive discussion of countermeasures like shuffling, masking, and DPA-resistant logic styles to decide how to protect smart cards.The basic power attack is presented: simple power analysis. It directly exploits the dependency between the power consumption (i.e. patterns in the power trace) and secret information.
Power analysis attacks : revealing the secrets of smart cards. 1. Introduction -- 2. Cryptographic devices -- 3. Power consumption -- 4. Statistical characteristics of power traces -- 5. Simple power analysis -- 6. Differential power analysis -- 7. Hiding -- 8.
The first comprehensive discussion of power analysis attacks on smart cards. Examples and case studies illustrate the various attacks, from simple to differential power-analysis attacks. Detailed descriptions and comparisons of the effectiveness of different countermeasures. Power Analysis Attacks: Revealing the Secrets of Smart Cards is the first comprehensive treatment of power analysis attacks and countermeasures. Based on the principle that the. Power Analysis Attacks: Revealing the Secrets of Smart Cards provides a unified overview and comparison of power analysis attacks. Illustrative examples and case studies are used throughout the monograph to explain the attacks and compare the effectiveness of the different countermeasures.
\Power Analysis Attacks: Revealing the Secrets of Smart Cards"
This volume explains how power analysis attacks work and provides an extensive discussion of countermeasures like shuffling, masking, and DPA-resistant logic styles to decide how to protect smart cards. Power analysis attacks .Power analysis attacks allow the extraction of secret information from smart cards. Smart cards are used in many applications including banking, mobile communications, pay TV, and electronic signatures. In all these applications, the security of the smart cards is of crucial importance.
Power Analysis Attacks - Revealing the Secrets of Smart Cards — Graz University of Technology. Stefan Mangard, Maria Elisabeth Oswald, Thomas Popp. Institute of Applied Information Processing and Communications (7050) Research output: Book/Report › Book. Overview. Projects (6) Treatment code (Nähere Zuordnung) Application. Theoretical.
Power Analysis Attacks: Revealing the Secrets of Smart Cards is the first comprehensive treatment of power analysis attacks and countermeasures. Based on the principle that the.
Power analysis attacks : revealing the secrets of smart cards
smart card vs emv

smart card vs sd card
Power Analysis Attacks: Revealing the Secrets of Smart Cards
Find great deals on eBay for Nintendo 3DS Nfc Reader Writer for. Shop with confidence. Skip .XP. 772. Country. Mar 10, 2017. #14. cathtbh said: Using blank NTAG215 NFC .
power analysis attacks on smart cards|\Power Analysis Attacks: Revealing the Secrets of Smart Cards"