how to read encrypted rfid cards NFC chip cards used for payments are programmed to emulate the same 79 characters that you might find on a mag stripe card, with a couple of exceptions: they can listen for variable data transmitted by the reader, they can respond with whatever the chip is programmed to send, and each card contains a secret key that is known only to the bank . App can then use the “add to wallet” button to save the passes As long as the readers you’re .
0 · what is a rfid card
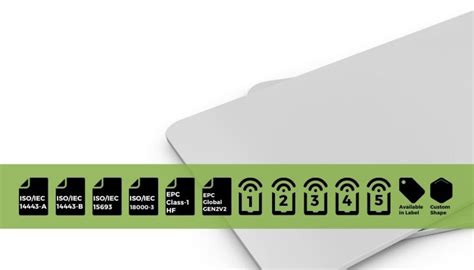
1 · types of rfid cards
2 · rfid card instructions for beginners
3 · how to use rfid cards
4 · how rfid cards work
5 · can rfid cards be hacked
6 · basics of rfid cards
7 · barcode rfid card
Information on the Apple iPhone XS Max's NFC function. Includes which NFC tags work best and whether you need an App to be able to read/write NFC tags. . With iOS 13, the iPhone XS Max can now read the UID of the tags and .
what is a rfid card
NFC chip cards used for payments are programmed to emulate the same 79 characters that you might find on a mag stripe card, with a couple of . Key Considerations For Successfully Safeguarding Your RFID Card. Taking it to the Next Level in RFID Technology: How to Encrypt RFID Data. Alternatives to Traditional RFID Cards. Wrapping Up and My Experience With . How to decode the encrypted mifare ic card/decoding rfid tag 13.56mhz. Zoco RFID. 179 subscribers. Subscribed. 22. 8.1K views 2 years ago. Buy from https://s.click.aliexpress.com/e/_oDi..more .
NFC chip cards used for payments are programmed to emulate the same 79 characters that you might find on a mag stripe card, with a couple of exceptions: they can listen for variable data transmitted by the reader, they can respond with whatever the chip is programmed to send, and each card contains a secret key that is known only to the bank . Key Considerations For Successfully Safeguarding Your RFID Card. Taking it to the Next Level in RFID Technology: How to Encrypt RFID Data. Alternatives to Traditional RFID Cards. Wrapping Up and My Experience With RFID Cards and Common Applications of .
what do nfc smart tags do
How to decode the encrypted mifare ic card/decoding rfid tag 13.56mhz. Zoco RFID. 179 subscribers. Subscribed. 22. 8.1K views 2 years ago. Buy from . One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way .
To best demonstrate the power and versatility of this tool, we will be reading, decrypting, and emulating a proprietary Mifare 1k hotel room key card using the only the Proxmark3 RDV4 with Blue Shark Module, the default antenna set, and an . READ/WRITE/DECREMENT/INCREMENT – always sent in encrypted session. TRANSFER – writes the result of one of the previous operations to non-volatile memory. RESTORE – prepares the current value of blocks to be over-written. Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time.
I just got an RFID/NFC implant. I got the "NeXt" from Dangerous Things so it has support for both RFID and NFC. I know that you can order one of those RFID cloners from china (which I've already ordered) if you want to clone an RFID card but how would you go about cloning an encrypted NFC tag?The only thing we can do without the keys of a card is to read its UID and ATQ. Q: Are the RFID ISO/IEC 14443-A/Mifare® standards a 100% secure system? A: No. Any security system has bugs that can be hacked. Besides, there are "security enhancers" integrated chips for RFID/NFC that Libelium does not implement. I am trying to use this encryption library for RFID Tags, AESLib - Arduino Reference. I cannot find any example online or documentation that actually help me understand how to use it. NFC chip cards used for payments are programmed to emulate the same 79 characters that you might find on a mag stripe card, with a couple of exceptions: they can listen for variable data transmitted by the reader, they can respond with whatever the chip is programmed to send, and each card contains a secret key that is known only to the bank .
Key Considerations For Successfully Safeguarding Your RFID Card. Taking it to the Next Level in RFID Technology: How to Encrypt RFID Data. Alternatives to Traditional RFID Cards. Wrapping Up and My Experience With RFID Cards and Common Applications of .
How to decode the encrypted mifare ic card/decoding rfid tag 13.56mhz. Zoco RFID. 179 subscribers. Subscribed. 22. 8.1K views 2 years ago. Buy from . One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way .To best demonstrate the power and versatility of this tool, we will be reading, decrypting, and emulating a proprietary Mifare 1k hotel room key card using the only the Proxmark3 RDV4 with Blue Shark Module, the default antenna set, and an . READ/WRITE/DECREMENT/INCREMENT – always sent in encrypted session. TRANSFER – writes the result of one of the previous operations to non-volatile memory. RESTORE – prepares the current value of blocks to be over-written.
Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time. I just got an RFID/NFC implant. I got the "NeXt" from Dangerous Things so it has support for both RFID and NFC. I know that you can order one of those RFID cloners from china (which I've already ordered) if you want to clone an RFID card but how would you go about cloning an encrypted NFC tag?The only thing we can do without the keys of a card is to read its UID and ATQ. Q: Are the RFID ISO/IEC 14443-A/Mifare® standards a 100% secure system? A: No. Any security system has bugs that can be hacked. Besides, there are "security enhancers" integrated chips for RFID/NFC that Libelium does not implement.
types of rfid cards
rfid card instructions for beginners
what kinds of data can be shared with nfc tags
$39.00
how to read encrypted rfid cards|what is a rfid card