security vulnerabilities of rfid tags In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security.
List via AuburnTigers.com of radio stations across the South that air Auburn football games.. Auburn Football Radio Affiliates {}Abbeville WESZ-FM 98.7 {}Greenville .
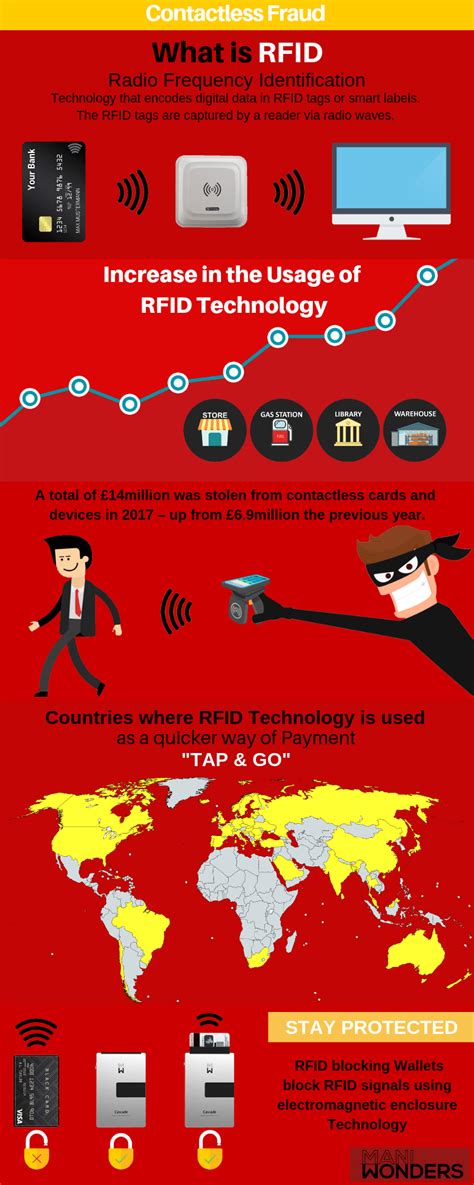
0 · rfid scammers
1 · rfid scam
2 · rfid laws and regulations
3 · rfid how to block
4 · problems with rfid technology
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
No matter what happened on that play, Nov. 30, 2013, was probably going to go down as one of the greatest Iron Bowls in the rivalry’s long history. No. 4 Auburn entered 10-1, and No. 1 Alabama .
rfid scammers
contactless prime credit card amazon
Identifying vulnerabilities in RFID-related physical controls is crucial for .With the increasing use of RFID technology, it is crucial to recognize the importance of cybersecurity. As objects become more interconnected, they also become vulnerable to cyber attacks. Imagine if a hacker could gain unauthorized access to . Identifying vulnerabilities in RFID-related physical controls is crucial for organizations to protect valuable assets, prevent system disruptions, comply with regulations and standards, and ensure the security, privacy, reliability, and integrity of RFID systems. Today, the Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), National Security Agency (NSA), and international partners released joint Cybersecurity Advisory, 2023 Top Routinely Exploited Vulnerabilities. This advisory supplies details on the top Common Vulnerabilities and Exposures (CVEs) routinely exploited .
But this terahertz tag shared a major security vulnerability with traditional RFIDs: A counterfeiter could peel the tag off a genuine item and reattach it to a fake, and the authentication system would be none the wiser.
In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security.RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities.RFID has a number of technical limitations and built-in vulnerabilities that create issues for security professionals. Basic RFID tags, especially the low-frequency variety, don’t possess any sort of data encryption at the source. RFID communication protocols offer protection against tag tracking, replay attacks, and cloning attacks, among others, enabling a balance between security and high effi- ciency
Researchers at the Vrije Universiteit Amsterdam have found that RFID tags have the characteristics that can be used to exploit vulnerabilities in databases and middleware of RFID implementations. They provided a Proof of Concept by writing malware to an RFID tag (see: rfid_malware.dvi (vu.nl) ).
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.With the increasing use of RFID technology, it is crucial to recognize the importance of cybersecurity. As objects become more interconnected, they also become vulnerable to cyber attacks. Imagine if a hacker could gain unauthorized access to . Identifying vulnerabilities in RFID-related physical controls is crucial for organizations to protect valuable assets, prevent system disruptions, comply with regulations and standards, and ensure the security, privacy, reliability, and integrity of RFID systems.
rfid scam
Today, the Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), National Security Agency (NSA), and international partners released joint Cybersecurity Advisory, 2023 Top Routinely Exploited Vulnerabilities. This advisory supplies details on the top Common Vulnerabilities and Exposures (CVEs) routinely exploited . But this terahertz tag shared a major security vulnerability with traditional RFIDs: A counterfeiter could peel the tag off a genuine item and reattach it to a fake, and the authentication system would be none the wiser.In this paper we analyze some of the most common types of attack on RFID tags: unauthorized disabling, unauthorized cloning, unauthorized tracking, and response replay. We introduce security mechanisms appropriate to defeat these attacks, and show how a recently proposed RFID authentication protocol uses them to achieve security.RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities.
RFID has a number of technical limitations and built-in vulnerabilities that create issues for security professionals. Basic RFID tags, especially the low-frequency variety, don’t possess any sort of data encryption at the source.
RFID communication protocols offer protection against tag tracking, replay attacks, and cloning attacks, among others, enabling a balance between security and high effi- ciency Researchers at the Vrije Universiteit Amsterdam have found that RFID tags have the characteristics that can be used to exploit vulnerabilities in databases and middleware of RFID implementations. They provided a Proof of Concept by writing malware to an RFID tag (see: rfid_malware.dvi (vu.nl) ).

Auburn's first, Auburn's best, and Auburn's favorite Sports Call-in radio program. Broadcasting LIVE from Auburn's own Tiger 93.9 FM.Auburn tree killer on why he poisoned the Toomer's Corner oak trees: “I wanted Auburn people to hate me as much as I hate them." An Alabama fan who poisoned Toomer’s .
security vulnerabilities of rfid tags|rfid how to block