smart card mitm MITM attacks often succeed by exploiting weak or misconfigured credential-based authentication methods like PEAP-MSCHAPv2. Using 802.1X with digital certificates eliminates credential-based vulnerabilities, providing strong encryption and authentication security.
A Smartcard (NFC) security validator that runs on Security devices running .
0 · what is a mitm attack
1 · mitm encryption
NFC is just a type of RFID. This covers a range of frequencies, formats, etc. NFC is just in the 13.56MHz band. I honestly thought Keysy covered both 125KHz and 13.56MHz like the Magic Ring. If you want something that covers both then Dangerous Things sells that sort of thing. A little out of reach personally but a guy can dream.
Generative AI is making MITM attacks more prevalent because it’s now easier to trick unsuspecting users into a phishing dragnet.
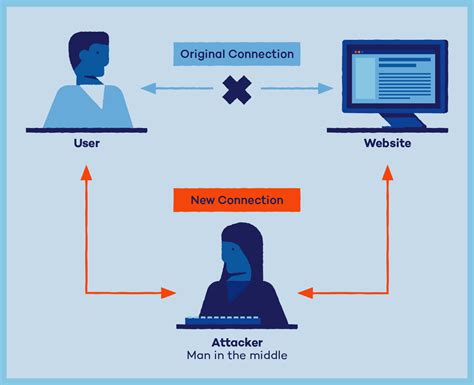
A man-in-the-middle (MitM) attack is a type of cyberattack in which communications between two parties is intercepted, often to steal login credentials or personal . The RDPDR channel is used for redirecting devices such as drives and smart cards from the client machine to the remote session. On the remote machine, the channel is handled by a filesystem driver that communicates with RDS over the TSVCPIPE pipe. Here’s a brief introduction to the protocol.
Generative AI is making MITM attacks more prevalent because it’s now easier to trick unsuspecting users into a phishing dragnet.
A man-in-the-middle (MitM) attack is a type of cyberattack in which communications between two parties is intercepted, often to steal login credentials or personal information, spy on.MITM attacks often succeed by exploiting weak or misconfigured credential-based authentication methods like PEAP-MSCHAPv2. Using 802.1X with digital certificates eliminates credential-based vulnerabilities, providing strong encryption and authentication security.An overview of man-in-the-middle (MITM) attacks: what they are, how they work, the damage they can do, and why passwords won't stop them.
A man-in-the-middle (MitM) attack is a form of cyberattack in which criminals exploiting weak web-based protocols insert themselves between entities in a communication channel to steal data. Here’s everything you need to know about MiTM schemes specifically, how to identify when your device is experiencing one, and how to protect your personally identifiable information (PII) and your device from cybercriminals.You can use several tools to test MITM attacks, such as a Wi-Fi pineapple, password-stealing tools, Kali Linux, MITMf, Wireshark, Cain &Abel, Ettercap, and additional tools like ARP spoofing, etc. Digital certificates help networks move away from credentials.
A man-in-the-middle (MitM) attack is a form of cyberattack where important data is intercepted by an attacker using a technique to interject themselves into the communication process. A man-in-the-middle attack (MITM attack) is a cyber attack where an attacker relays and possibly alters communication between two parties. The RDPDR channel is used for redirecting devices such as drives and smart cards from the client machine to the remote session. On the remote machine, the channel is handled by a filesystem driver that communicates with RDS over the TSVCPIPE pipe. Here’s a brief introduction to the protocol. Generative AI is making MITM attacks more prevalent because it’s now easier to trick unsuspecting users into a phishing dragnet.
A man-in-the-middle (MitM) attack is a type of cyberattack in which communications between two parties is intercepted, often to steal login credentials or personal information, spy on.MITM attacks often succeed by exploiting weak or misconfigured credential-based authentication methods like PEAP-MSCHAPv2. Using 802.1X with digital certificates eliminates credential-based vulnerabilities, providing strong encryption and authentication security.
what is a mitm attack
An overview of man-in-the-middle (MITM) attacks: what they are, how they work, the damage they can do, and why passwords won't stop them.A man-in-the-middle (MitM) attack is a form of cyberattack in which criminals exploiting weak web-based protocols insert themselves between entities in a communication channel to steal data. Here’s everything you need to know about MiTM schemes specifically, how to identify when your device is experiencing one, and how to protect your personally identifiable information (PII) and your device from cybercriminals.You can use several tools to test MITM attacks, such as a Wi-Fi pineapple, password-stealing tools, Kali Linux, MITMf, Wireshark, Cain &Abel, Ettercap, and additional tools like ARP spoofing, etc. Digital certificates help networks move away from credentials.
contactless card reader atm
A man-in-the-middle (MitM) attack is a form of cyberattack where important data is intercepted by an attacker using a technique to interject themselves into the communication process.
charles schwab contactless card
mitm encryption

MIFARE Partner Program - MIFARE: Contactless NFC Solutions | NXP .
smart card mitm|what is a mitm attack