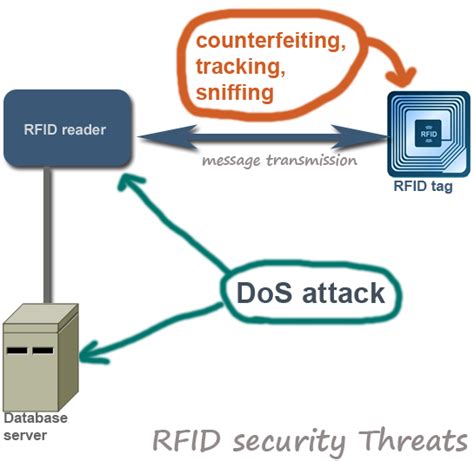
list some of the security concerns of an rfid system. current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this paper, we discuss four common types of RFID tag attacks . I have a NFC tag reader based on ST25R3911B and I'm currently using it to read .
0 · rfid security problems
1 · rfid privacy and security issues
2 · rfid is vulnerable to
3 · rfid disadvantages
4 · problems with rfid technology
5 · problems with rfid
6 · is rfid dangerous
7 · compliance issues with rfid bands
The Skylanders Portal Demystified. If you haven’t heard of the game Skylanders: Spyro’s Adventure, google it. It’s a video game for the PC/Mac, Wii, PS3, Xbox 360, and 3DS which .
From unauthorized access and data breaches to physical tampering and regulatory compliance, these security challenges highlight the importance of implementing proactive measures to . RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal money from your phone’s tap-to-pay app, or clone the chip and gain .
Security breaches in RFID systems can have serious consequences, including unauthorized access to sensitive information, theft of valuable assets, and disruption of essential operations. .Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID related security issues.current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this paper, we discuss four common types of RFID tag attacks .
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful. By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas. Part 2 examines some of the more common security and privacy concerns associated with RFID, primarily related to retail and consumer applications. What is RFID? This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
“Security issues in RFID system” presents various attacks possible on RFID devices. This section includes the attacks based on the CIA (confidentiality, integrity, and availability) properties of the RFID system. RFID systems are vulnerable to denial of service (DoS) attacks by disrupting communication between tags and readers. Malicious actors overwhelm these two with excessive data requests or signal interference.
However, RFID systems also raise serious privacy and security concerns. This article offers a brief review of the main threats to RFID systems and proposes a methodology for qualitatively evaluating the risk level for various application domains. Within less than a decade, a large number of research papers dealing with security issues of RFID technology have appeared. In this paper we want to provide some thoughts on security issues concerning RFID systems and to highlight some of the areas that have to be considered regarding this topic.Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID related security issues.
current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this paper, we discuss four common types of RFID tag attacks . Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful.
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas. Part 2 examines some of the more common security and privacy concerns associated with RFID, primarily related to retail and consumer applications. What is RFID? This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
rfid security problems
“Security issues in RFID system” presents various attacks possible on RFID devices. This section includes the attacks based on the CIA (confidentiality, integrity, and availability) properties of the RFID system. RFID systems are vulnerable to denial of service (DoS) attacks by disrupting communication between tags and readers. Malicious actors overwhelm these two with excessive data requests or signal interference.
current smart phone sd card reader
However, RFID systems also raise serious privacy and security concerns. This article offers a brief review of the main threats to RFID systems and proposes a methodology for qualitatively evaluating the risk level for various application domains.
rfid privacy and security issues

rfid is vulnerable to
iOS apps running on supported devices can use NFC scanning to read data from electronic tags attached to real-world objects. See more
list some of the security concerns of an rfid system.|problems with rfid