can rfid cards be hacked RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their . See more Here’s how you can access the NFC Tag Reader on your iPhone and use it not just for the payments but also for so may other things and automate a lot of tasks.Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put your iPhone near the NFC tag. Enter a name for your tag. .
0 · rfid scam
1 · problems with rfid technology
2 · problems with rfid
3 · is rfid safe to hack
4 · is rfid dangerous
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
Auburn, AL 36849 (334) 844-9345. Schedule; Connect; About Us; Read; .
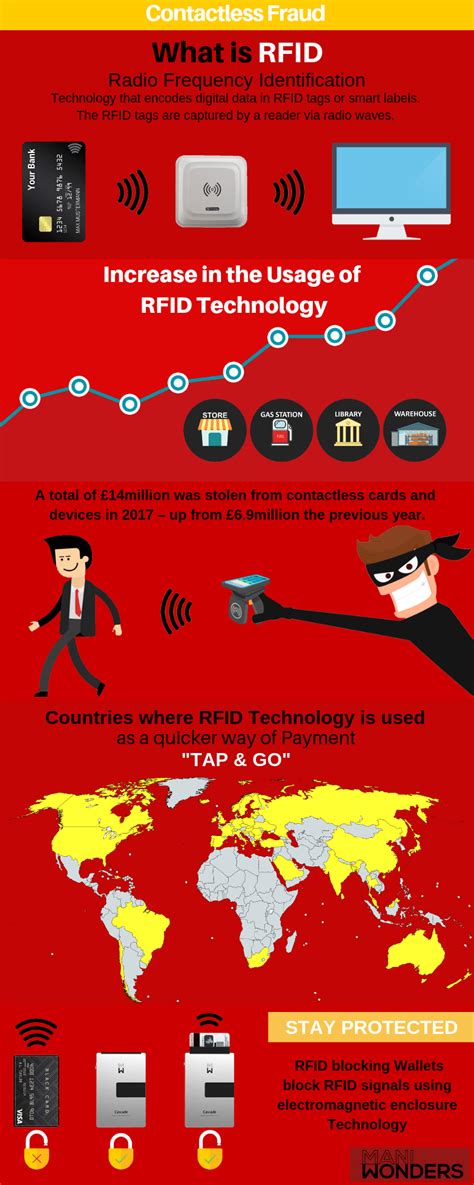
RFID stands for Radio Frequency Identification and it's used for short-distance communication of information. It does not require line of sight to work, meaning that the RFID chip and the reader merely need to be within range of each other to communicate. There are a few main types of RFID chip: 1. . See moreRFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their . See moreSo, if you do want to stay on the safe side, how do you block RFID signals? In general, metal and water are the best ways to block radio . See moreAs hackers have demonstrated, RFID is not impervious from attacks. There are cheap ways to build a scanner, at which point they can scan tags for sensitive information. While the panic around this form of attack may outshadow the actual chance that you'll . See more
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack .
Simply put, the computer chip in your EMV card does not transmit an RFID signal. That's because these cards don't offer contactless transactions.
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack . Simply put, the computer chip in your EMV card does not transmit an RFID signal. That's because these cards don't offer contactless transactions.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, .
Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. . The majority of attacks against RFID systems can be broken into three major categories: man-in-the-middle (MITM), cloning, and brute forcing. Man-in-the-Middle. An attack . Hacker Tool Teaches All About NFC And RFID. 29 Comments. by: Donald Papp. October 4, 2021. The Flipper Zero is a multipurpose hacker tool that aims to make the world of .Inadequate protection of RFID systems can lead to financial losses, compromised sensitive information, and damage to a company’s reputation. For instance, in 2014, a major retail chain .
Most experts agree that RFID theft is rare if non-existent in 2024. Credit card companies now claim that each card transaction is encrypted, requiring a one time token to . Keeping key cards in a reader proof wallet or case will help prevent skimming, where an attacker gets close enough with an NFC or RFID reader. Most importantly, physical .
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack .
Simply put, the computer chip in your EMV card does not transmit an RFID signal. That's because these cards don't offer contactless transactions.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, .
fixed uhf rfid reader
Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. . The majority of attacks against RFID systems can be broken into three major categories: man-in-the-middle (MITM), cloning, and brute forcing. Man-in-the-Middle. An attack .
Hacker Tool Teaches All About NFC And RFID. 29 Comments. by: Donald Papp. October 4, 2021. The Flipper Zero is a multipurpose hacker tool that aims to make the world of .Inadequate protection of RFID systems can lead to financial losses, compromised sensitive information, and damage to a company’s reputation. For instance, in 2014, a major retail chain . Most experts agree that RFID theft is rare if non-existent in 2024. Credit card companies now claim that each card transaction is encrypted, requiring a one time token to .
rfid scam
how to make rfid card
hid rfid card frequency
how to add a rfid card to apple wallet
esp rfid reader
Basic Functioning of NFC: NFC technology enables wireless communication over short distances, typically a few centimetres. It operates within the radio frequency (RF) spectrum at 13.56 MHz. When an NFC-enabled device, like a .
can rfid cards be hacked|how to stop rfid scanning