recommendations on rfid protection This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks. A critical feature of a genuine Rolex warranty card is an embedded NFC chip, which if you hold your phone to it, will take you to the Rolex website. It’s visible in the top right corner of the card as a tiny square, which you can see disrupting the .
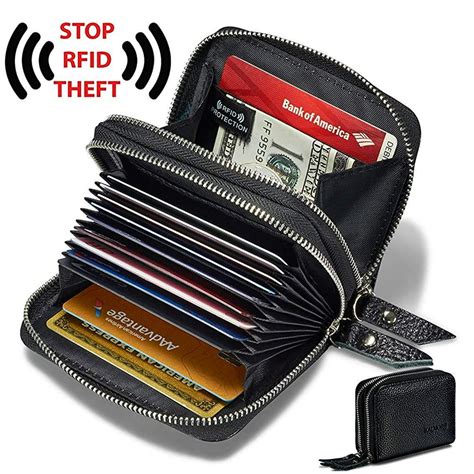
0 · women's wallets with rfid protection
1 · rfid wallets that actually work
2 · highest rated rfid blocking sleeves
3 · consumer reports rfid blocking wallets
4 · best rfid wallets consumer reports
5 · best rfid wallets 2024
6 · best rfid blocking material
7 · best rfid blocking card 2022
Step One: After launching Animal Crossing: New Horizons, head to the Nook Stop at Resident Services Step Two: Select “Invite a Camper” Step Three: Hold the amiibo card to the NFC touchpoint on .
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates .Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement authentication mechanisms to ensure that only authorized tags and readers can interact with each other.
Its list of recommended practices for ensuring the security and privacy of RFID systems includes: firewalls that separate RFID databases from an organization's other databases and information technology (IT) systems; encryption of radio signals when feasible; authentication of approved users of RFID systems;OECD Basic Principles: Guidelines on the Protection of Privacy and Transborder Flows of Personal Data..................................6-4
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
The best way to prevent eavesdropping is to adopt a layered security approach that prioritizes encryption and secure authentication protocols. Managers should ensure every RFID system within the supply chain uses end-to-end encryption to protect transmitted data.Use of RFID technology should be as transparent as possible, and consumers should know about the implementation and use of any RFID technology (including tags, readers and storage of PII) as they engage in any transaction that utilizes an RFID system. So how can you protect your sensitive data from falling into the wrong hands? In this article, we’ll discuss how uninvited parties might try to get ahold of your information and eight different ways you can prevent that from happening.
In this comprehensive article, we will delve deeply into how RFID is regulated worldwide, the global and regional standards in place, industry-specific considerations, and the future trends shaping RFID regulation.Explain the components, operation, and application of RFID technology. Understand the privacy implications with using RFID-embedded items. Differentiate across threat categories. Describe different security recommendations to secure RFID. This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement authentication mechanisms to ensure that only authorized tags and readers can interact with each other. Its list of recommended practices for ensuring the security and privacy of RFID systems includes: firewalls that separate RFID databases from an organization's other databases and information technology (IT) systems; encryption of radio signals when feasible; authentication of approved users of RFID systems;OECD Basic Principles: Guidelines on the Protection of Privacy and Transborder Flows of Personal Data..................................6-4
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! The best way to prevent eavesdropping is to adopt a layered security approach that prioritizes encryption and secure authentication protocols. Managers should ensure every RFID system within the supply chain uses end-to-end encryption to protect transmitted data.
Use of RFID technology should be as transparent as possible, and consumers should know about the implementation and use of any RFID technology (including tags, readers and storage of PII) as they engage in any transaction that utilizes an RFID system. So how can you protect your sensitive data from falling into the wrong hands? In this article, we’ll discuss how uninvited parties might try to get ahold of your information and eight different ways you can prevent that from happening.In this comprehensive article, we will delve deeply into how RFID is regulated worldwide, the global and regional standards in place, industry-specific considerations, and the future trends shaping RFID regulation.
women's wallets with rfid protection
rfid wallets that actually work
highest rated rfid blocking sleeves
About Credit Card Reader NFC (EMV) 5.5.1. This app was designed to allow users to read the public data stored on their NFC-compliant EMV banking cards, such as credit .
recommendations on rfid protection|best rfid wallets consumer reports