smart card encryption algorithm In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between these algorithms to find out the differences. These cards are made to order, so they are always in stock! Each card is a fully functional Animal Crossing amiibo. All designs are custom made by me the owner of Teddymuffs Designs. I've used PVC NFC cards with my design adhered to .
0 · Smart card
1 · All about encryption in smart card
2 · (PDF) Lightweight Cipher Algorithms for Smart Cards
Add your unique wCard.io URL to all the platforms and places you find your audience. Use .Award-winning sustainable Digital Business Cards, Review Tags, Table Talkers, NFC Tags & .
Smart card
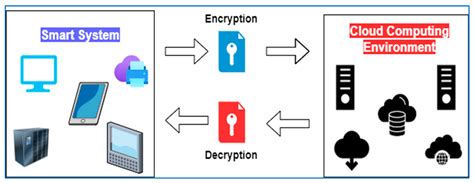
In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between these algorithms to find out the differences.In this paper, smart cards applications and its security threats are discussed. The .

how to use the rfid tag in trucking
Smart cards serve as credit or ATM cards, fuel cards, mobile phone SIMs, authorization cards for pay television, household utility pre-payment cards, high-security identification and access badges, and public transport and public phone payment cards. Smart cards may also be used as electronic wallets. The smart card chip can . In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between . In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between these algorithms to find out the differences.
The most widely used cryptographic algorithms in smart cards (excluding the GSM so-called "crypto algorithm") are Triple DES and RSA. The key set is usually loaded (DES) or generated (RSA) on the card at the personalization stage. In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between these algorithms to find.
This article presents an update on recent developments in the area of cryptographic algorithms that are relevant for smart cards. It includes a review of the status of hash functions, block ciphers and stream ciphers and presents an update on authenticated or .In this paper, smart cards applications and its security threats are discussed. The smart cards authentication and data encryption schemes have been surveyed which lead to comparative survey of various works proposed in this area. This survey results in some research issues; and future directions to resolve these issues are defined.The answers to the above question explain that the chip based cards can not be cloned as the "secret number" is embedded in the chip and protected by the use of public key cryptography. The chip also performs some cryptographic operations to authenticate itself without revealing the actual secret information.
Successful attacks against smart cards have included power glitching; differential power analysis; and capping them then using an ion-beam microscope to read out the key bits from the flash memory. Because the cards are always at risk of being stolen by an advanced attacker, each card is usually issued a unique key. This article presents an overview of the cryptographic primitives that are commonly implemented on smart cards. We will also discuss attacks that can be mounted on smart cards. Besides cryptographic attacks on the algorithms, smart cards are also vulnerable to attacks that exploit weaknesses in the implementations. Typical examples are timing .The micro coded cryptography processor is designed for smart card applications, supporting both private key and public key algorithms while meeting the required power and performance standards. Impressively, it is as small as 2.25 mm2 using 0.18-μm 6LM CMOS technology.A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for the purpose of authentication. Users connect their smart card to a host computer.
In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between these algorithms to find out the differences.The most widely used cryptographic algorithms in smart cards (excluding the GSM so-called "crypto algorithm") are Triple DES and RSA. The key set is usually loaded (DES) or generated (RSA) on the card at the personalization stage. In this paper we are going to describe the most popular and efficient encryption algorithms in smart cards such as RSA, ECC, DES and ECDSA and comparisons between these algorithms to find. This article presents an update on recent developments in the area of cryptographic algorithms that are relevant for smart cards. It includes a review of the status of hash functions, block ciphers and stream ciphers and presents an update on authenticated or .
In this paper, smart cards applications and its security threats are discussed. The smart cards authentication and data encryption schemes have been surveyed which lead to comparative survey of various works proposed in this area. This survey results in some research issues; and future directions to resolve these issues are defined.The answers to the above question explain that the chip based cards can not be cloned as the "secret number" is embedded in the chip and protected by the use of public key cryptography. The chip also performs some cryptographic operations to authenticate itself without revealing the actual secret information. Successful attacks against smart cards have included power glitching; differential power analysis; and capping them then using an ion-beam microscope to read out the key bits from the flash memory. Because the cards are always at risk of being stolen by an advanced attacker, each card is usually issued a unique key.
This article presents an overview of the cryptographic primitives that are commonly implemented on smart cards. We will also discuss attacks that can be mounted on smart cards. Besides cryptographic attacks on the algorithms, smart cards are also vulnerable to attacks that exploit weaknesses in the implementations. Typical examples are timing .The micro coded cryptography processor is designed for smart card applications, supporting both private key and public key algorithms while meeting the required power and performance standards. Impressively, it is as small as 2.25 mm2 using 0.18-μm 6LM CMOS technology.
All about encryption in smart card
(PDF) Lightweight Cipher Algorithms for Smart Cards
how to read user memory information from rfid reader
$69.98
smart card encryption algorithm|Smart card